Snowden leak exposes US plan to spy on foreign businesses for profit
A 2009 intelligence document provided to journalists by former government contractor Edward Snowden suggests the United States weighed someday conducting espionage to prevent losing its economic prowess to other countries.
The document, published first by The Intercept on Friday this week, outlines tactics the American intelligence community may implement in the future in the event of certain scenarios, including one in which “the United States’ technological and innovative edge slips” in the year 2025.
In the event that the US may lose that advantage, the Quadrennial Intelligence Community Review’s final report reads in part, then “a multi-pronged, systematic effort to gather open source and proprietary information through overt means, clandestine penetration (through physical and cyber means) and counterintelligence” could be undertaken by American agencies.
The document, classified as “secret” and supplied along with a trove of other files provided by Snowden,“is a fascinating window into the mindset of America’s spies as they identify future threats to the US and lay out the actions the US intelligence community should take in response,” wrote Glenn Greenwald, The Intercept editor who wrote about the 32-page report this week.
Indeed, David Shredd, then the deputy director of national intelligence, opens the report by describing it as the results of a 10-month study conducted among experts from agencies, academia, think tanks and industry tasked with assessing the implications of the year 2025 for the American intelligence community, or IC.
“If one does not consider the long-range future, one will never cease to be surprised,” Shredd wrote. “QICR 2009 developed alternative future scenarios based on Global Trends 2025 to explore concepts and capabilities the IC may need to fulfill critical missions in support of US national security.”
The contents of the report, Shredd added, “does not purport that any one future will materialize, but rather outlines a range of plausible futures so that the IC can best posture itself to meet the range of challenges it may face.” Speaking to The Intercept, a spokesperson for the Office of the Director of National Intelligence said the report “is not intended to be, and is not, a reflection of current policy or operations.”
Jeffrey Anchukaitis, the DNI spokesperson, told Greenwald that “the United States — unlike our adversaries—does not steal proprietary corporate information to further private American companies’ bottom lines,” and that “the Intelligence Community regularly engages in analytic exercises to identify potential future global environments, and how the IC could help the United States Government respond.”
Nevertheless, the report contains potential plans of action that run counter to previous public admissions made by IC leaders.
“What we do not do, as we have said many times, is use our foreign intelligence capabilities to steal the trade secrets of foreign companies on behalf of — or give intelligence we collect to—US companies to enhance their international competitiveness or increase their bottom line,” Greenwald quoted Director of National Intelligence James Clapper as saying previously.
“But asecret 2009 report issued by Clapper’s own officeexplicitly contemplates doing exactly that,” the journalist wrote this week.
“The IC would need the ability to access proprietary sources of information in permissive environments such as foreign universities, industry trade shows and government conferences,” part of the report reads. “This could include cooperating US students, professors and researchers reporting bits of non-public information that by themselves are not sensitive, but in aggregate could help the IC make inferences about breakthrough technological innovations. The key challenge would be working closely with the academic and scientific communities (which would include non-US persons), gaining trust and monitoring potential 'threats' while continuing to advance US scientific progress.”
According to the document, human spies and cyber operations alike have been considered as possible tools to implement if spying on foreign targets — and not just students and innovators, but entire research and development operations, as well—is needed to be done in 11 years’ time.
“In denied or more restrictive environments such as state-supported R&D centers, the IC would continue to apply human intelligence (HUMINT) tradecraft and employ HUMINT-enabled close access collection. This would include recruitment of sources and assets, and provision of appropriate technical means to acquire and exfiltrate sensitive information,” reads one part of the document.
Elsewhere, the document’s authors detail one end goal: “Technology acquisition by all means.”
“Exfiltrating intelligence from non-permissive environments will be crucial. A critical enabler would be covert communications with a negligible forward footprint. US intelligence officers and sensitive sources will need to move data in an unattributable and undetected way, sometimes from within commercial entities possessing great technical prowess and robust cyber and electronic security protective procedures. Although the likely advent of transnational, high-bandwidth wireless communications services will offer an environment with ‘lots to hide behind,’ it will also contain many highly competent, and potentially antagonistic, actors.”
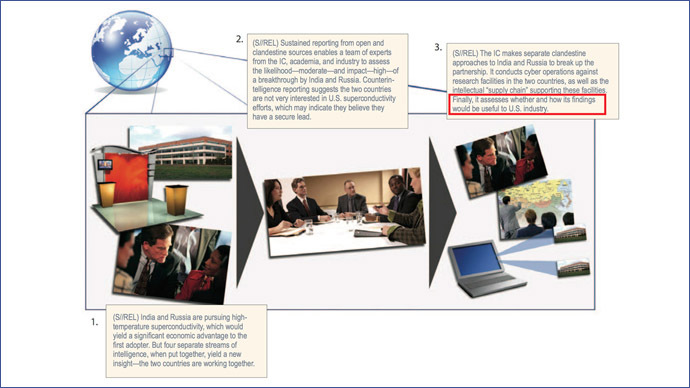
An illustrate example included in part of the report provides exactly how such a hypothetical situation may play out: “The IC makes separate clandestine approaches to India and Russia to break up the partnership. It conducts cyber operations against research facilities in the two countries, as well as the intellectual ‘supply chain’ supporting these facilities. Finally, it assesses whether and how its findings would be useful to US industry.”
“Using covert cyber operations to pilfer ‘proprietary information’ and then determining how it ‘would be useful to US industry’ is precisely what the US government has been vehemently insisting it does not do,” Greenwald wrote, “even though for years it has officially prepared to do precisely that.”














